TLS for Firefox on Windows
TLS Positive Overrides
Firefox for Windows can be used with Namecoin for TLS positive overrides; this allows certificates for .bit domains that match the blockchain to be used without errors. Instructions:
- Find your Firefox profile folder; it will usually be a subfolder of
%APPDATA%/Mozilla/Firefox/Profiles. For example,%APPDATA%/Mozilla/Firefox/Profiles/r3a8ono6.default. Note that you must use forward slashes, not backslashes. - Make sure that your Firefox profile folder is readable and writeable by the user who is running ncdns. If you installed ncdns via the installer, ncdns is run by the user
NT SERVICE\ncdns. -
Add the following to
ncdns.conf, substituting your Firefox profile folder for$PROFILEDIR:[tlsoverridefirefox] sync=true profiledir="$PROFILEDIR" - Restart ncdns.
TLS positive overrides will only be synchronized to Firefox while Firefox is not running; this means that, every so often, you should close Firefox for a few minutes and then re-open it.
You can now visit in Firefox a .bit website that supports TLS, e.g. the Namecoin forum’s .bit domain. The website should load in Firefox without errors.
TLS Negative Overrides
Firefox for Windows can be used with Namecoin for TLS negative overrides; this prevents malicious or compromised public CA’s from issuing certificates for .bit domains. Instructions:
Important warning for users of TLS intercepting proxies: these instructions will probably cause your intercepting proxy to produce an HPKP error for HTTPS websites that use HPKP. Right now, Namecoin TLS negative overrides for Firefox are not compatible with TLS intercepting proxies that try to intercept HPKP-enabled websites. If you haven’t deliberately installed a TLS intercepting proxy, or if you don’t know what a TLS intercepting proxy is, you can probably ignore this warning.
Note: Installing Namecoin TLS negative overrides for Firefox might cause previously-unnoticed attacks against you, e.g. from malicious surveillance infrastructure, to produce visible errors (even if those attacks are trying to intercept non-Namecoin connections).
- Go to
about:configin Firefox. - Search for
security.cert_pinning.enforcement_level. - Double-click the
security.cert_pinning.enforcement_levelpreference. - Enter
2and click OK. - Search for
security.cert_pinning.process_headers_from_non_builtin_roots. - Double-click the
security.cert_pinning.process_headers_from_non_builtin_rootspreference until theValuecolumn saystrue. - Close the
about:configtab in Firefox. - Restart Firefox.
- Install the Visual C++ 2010 Redistributable Package.
- Install the Visual C++ 2015 Redistributable Package.
- Download
mar-tools-win32.zipormar-tools-win64.zip(depending on whether you’re on 32-bit or 64-bit Windows) from Tor’s download page. - Extract the following files from the
mar-toolszip to a newmar-tools-32ormar-tools-64(depending on whether you’re on 32-bit or 64-bit Windows) subdirectory of the directory wheretlsrestrict_nss_tool.exeis:certutil.exefreebl3.dllmozglue.dllnss3.dllnssdbm3.dllsoftokn3.dll
- Rename
certutil.exetonss-certutil.exe. - To recap, if
tlsrestrict_nss_tool.exeis inC:\Users\Edward\Downloads\tlsrestrict_nss_tool.exeon 64-bit Windows, then there should also beC:\Users\Edward\Downloads\mar-tools-64\nss-certutil.exe. - Create a temporary directory; make sure that it only is readable/writeable by a user whom you trust with access to the Firefox certificate database. Note its path; make sure you use forward-slashes instead of backslashes, and leave off the trailing slash.
- Find your NSS directory; it will usually be a subdirectory of
%APPDATA%/Mozilla/Firefox/Profiles. For example,%APPDATA%/Mozilla/Firefox/Profiles/r3a8ono6.default. Make sure you use forward-slashes instead of backslashes, and leave off the trailing slash. - Find the directory where
nssckbi.dllis located. This will usually beC:/Program Files/Mozilla Firefox. Make sure you use forward-slashes instead of backslashes, and leave off the trailing slash. -
Run the following, substituting the temporary directory, NSS directory, and CKBI directory for
$TEMP_DIR,$NSS_DIR, and$CKBI_DIR:tlsrestrict_nss_tool.exe "--tlsrestrict.nss-temp-db-dir=$TEMP_DIR" "--tlsrestrict.nss-dest-db-dir=$NSS_DIR" "--tlsrestrict.nss-ckbi-dir=$CKBI_DIR" - Wait a few minutes for
tlsrestrict_nss_toolto finish running.
You’ll need to rerun the above tlsrestrict_nss_tool command whenever the built-in certificate list is updated. You won’t need to redo the about:config steps, though.
If you’ve manually imported any non-built-in TLS trust anchors to Firefox, and you want to restrict them from intercepting .bit traffic, you should do the following for each such trust anchor:
- Get a DER-encoded certificate of the trust anchor.
-
Run the following, substituing the path to your trust anchor certificate for
$CERT_PATH:cross_sign_name_constraint_tool.exe "--cert.input-root-ca-path=$CERT_PATH" - 3 new certificates will be created:
root.crt,intermediate.crt, andcross-signed.crt. - Delete the existing trust anchor from Firefox.
- Import
root.crtinto Firefox; mark it as a trusted TLS root CA. - Import
intermediate.crtandcross-signed.crtinto Firefox; do not mark them as trusted.
If you decide later that you want to remove the negative overrides from Firefox, follow these instructions:
-
Run the following:
tlsrestrict_nss_tool.exe "--tlsrestrict.nss-temp-db-dir=$TEMP_DIR" "--tlsrestrict.nss-dest-db-dir=$NSS_DIR" "--tlsrestrict.nss-ckbi-dir=$CKBI_DIR" --tlsrestrict.undo - Wait a few minutes for
tlsrestrict_nss_toolto finish running. - If you want to restore compatibility with TLS intercepting proxies, follow these steps. If you don’t want to use a TLS intercepting proxy, or if you don’t know what a TLS intercepting proxy is, you probably don’t need to do this.
- Go to
about:configin Firefox. - Search for
security.cert_pinning.enforcement_level. - Right-click the
security.cert_pinning.enforcement_levelpreference. - Click
Reset. - Search for
security.cert_pinning.process_headers_from_non_builtin_roots. - Right-click the
security.cert_pinning.process_headers_from_non_builtin_rootspreference. - Click
Reset. - Close the
about:configtab in Firefox. - Restart Firefox.
- Go to
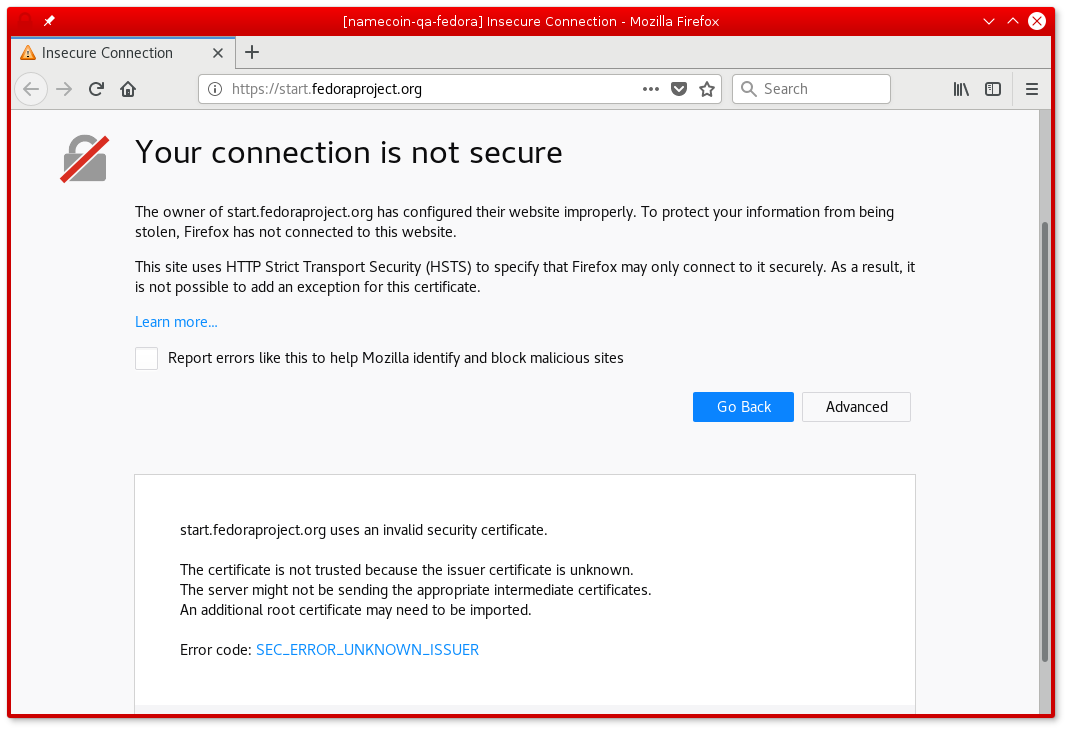
Screenshot
If a .bit HTTPS website uses a CA-signed certificate that doesn’t match the Namecoin blockchain, an error like this will be displayed: